Introduction to Billing Schemes and Accounting Fraud
- Billing Schemes and Accounting Fraud: Represent one of the most devastating forms of asset misappropriation confronting modern organizations, creating median losses of $100,000 per occurrence.
- Prevalence and Impact: The Association of Certified Fraud Examiners’ in their 2024 Occupation Fraud report establishes that billing schemes account for 22% of all asset misappropriation cases. This positions them among the most destructive internal fraud schemes threatening business financial integrity.
- Small Business Vulnerability: The risk proves particularly acute for smaller organizations, where billing fraud schemes constitute the second most common type of asset misappropriation. These schemes affect approximately 13% of all fraud cases in companies with fewer than one hundred employees.
- Escalating Threat Levels: Recent analysis reveals billing fraud increased by 6% in the first quarter of 2022 compared to the previous year. The extended detection period compounds the damage—these schemes typically operate undetected for 14 months, generating losses of approximately $8,300 monthly.
- Dangerous Financial Exposure: Billing schemes create particularly severe risks because they exploit the purchasing cycle where organizations process the majority of their payments. This structural vulnerability allows perpetrators to conceal larger thefts through false-billing schemes than through other fraudulent payment methods.
- Organizational Cost: Research demonstrates that organizations lose 5% of annual revenue to fraud, with median losses reaching $125,000. These staggering figures underscore the critical need for robust internal controls and comprehensive fraud prevention strategies.
- Essential Protection Framework: This guide examines the sophisticated techniques underlying billing schemes, documented case studies, warning signs, and proven prevention methodologies. Understanding these fraud risk factors empowers organizations to implement essential internal controls, strengthen corporate governance practices, and maintain regulatory compliance necessary to protect against these costly deceptions.
- Advanced Detection Strategies: Organizations must also deploy cutting-edge detection technologies and analytical approaches to counter evolving billing fraud tactics in 2026 and beyond. The investment in comprehensive fraud prevention proves far less costly than the devastating losses that result from undetected asset misappropriation.

Understanding Billing Schemes in Accounting Fraud
- Billing schemes: Constitute a primary mechanism through which employees execute asset misappropriation, requiring systematic analysis of their operational framework, classification within fraud hierarchies, and detection characteristics.
- Sophisticated Threat: These schemes exploit fundamental vulnerabilities in organizational purchasing processes, creating pathways for substantial financial losses that demand comprehensive understanding and targeted prevention strategies.
Definition of Billing Schemes and Accounting Fraud
- Fraudulent Disbursement Mechanism: Billing schemes occur when employees manipulate organizational payment systems by submitting invoices for fictitious goods or services, inflated charges, or personal purchases. These deceptive practices systematically exploit weaknesses in purchasing and accounts payable processes, enabling unauthorized fund transfers.
- Association of Certified Fraud Examiners Classification: The definitive framework identifies billing schemes as fraudulent disbursement techniques involving submission of bills for:
-
- Bogus goods or services designed to appear legitimate
- Inflated invoices that exceed actual costs or quantities
- Personal purchases disguised as legitimate business expenses
- Financial Impact Analysis: These schemes generate median losses of $100,000 per incident, establishing them as significant threats to organizational financial stability. The 2024 Report to the Nations confirms billing schemes represent 22% of all asset misappropriation cases throughout the United States.
How Billing Schemes Fit into Asset Misappropriation
- Fraudulent Disbursements: Within the asset misappropriation hierarchy, fraudulent disbursements constitute the most prevalent form of asset theft. Billing fraud schemes occupy a critical position within this category, directly targeting organizational purchasing functions.
- Organizational Payment Exploitation: These schemes compel businesses to issue payments for:
-
- Non-existent goods or services that were never delivered
- Overpriced products exceeding fair market value
- Unnecessary purchases serving no legitimate business purpose
- Cash Flow Impact: This fraud type creates substantial organizational cash flow disruption. Billing schemes enable perpetrators to conceal larger thefts through the purchasing cycle, which processes the majority of business payments.
- Primary Scheme Categories:
-
- Shell Company Schemes: Employees establish fictitious companies and submit invoices for payment
- Pay-and-Return Schemes: Employees overbill vendors to intercept overpayment refunds
- Personal Purchase Schemes: Employees submit personal invoices for company payment
On-Book vs Off-Book Fraud Schemes
- Detection Framework: The distinction between on-book and off-book fraud provides essential insights into detection challenges and prevention methodologies.
- On-Book Fraud Characteristics: These schemes occur after recording money on victim company books. Billing schemes fall within this category because fraudulent payments exit the organization while appearing in accounting records, establishing audit trails. This documentation creates detection opportunities through systematic financial record examination.
- On-book billing manifestations include:
-
- Shell company invoicing documented in financial systems
- Duplicate payments recorded in accounts payable
- Personal purchases processed through company accounting systems
- Off-Book Fraud Distinctions: These schemes execute before transaction recording in accounting systems. Examples include skimming incoming payments or inventory theft before documentation. Off-book frauds prove substantially more difficult to detect because they generate no traceable accounting evidence.
- Strategic Detection Implications: Different fraud categories require distinct detection approaches. On-book schemes may be identified through financial statement analysis and audit trail examination, while off-book schemes typically require surveillance, invigilation, and admission-seeking interviews.
- Multi-Layered Defense Requirements: Billing schemes present sophisticated threats to organizational assets that demand comprehensive detection and prevention frameworks. Understanding their operational mechanisms, relationship to asset misappropriation, and documentation characteristics establishes the foundation for effective countermeasures against these costly fraudulent disbursement techniques.
Eight Sophisticated Billing Schemes Devastating Organizations in 2025
Fraudulent Billing Practices: Continue evolving as perpetrators develop increasingly sophisticated methods to exploit organizational vulnerabilities. These schemes represent systematic attacks on asset misappropriation controls that can destroy financial integrity and trigger substantial losses.
Evolving Threat Landscape: Organizations confront unprecedented risks from billing schemes that exploit both technological advances and traditional control weaknesses to drain resources systematically.
Shell Company Invoicing: The Foundation of Deceptive Payments
Shell Companies: Serve as sophisticated vehicles for billing fraud, operating as empty entities with no physical presence, employees, or legitimate business operations. These fraudulent structures enable systematic theft through fabricated invoice submission.
Operational Mechanisms:
Entity Creation: Perpetrators establish business entities that appear legitimate through proper documentation while maintaining no actual operations.
Vendor Integration: Shell companies gain access to organizational payment systems through addition to approved vendor lists.
Invoice Submission: Fraudsters submit invoices for generic services like “consulting” that prove difficult to verify.
Payment Interception: Funds flow directly to perpetrator-controlled addresses and bank accounts.
Deceptive Naming Conventions: Shell companies frequently employ initial-based names such as ABC Services, Inc. to project professional legitimacy while maintaining generic identity. These entities often operate within “secrecy jurisdictions” that obscure beneficial ownership information, making fund tracing extremely difficult.
Pay-and-Return Schemes: Exploiting Vendor Relationships
- Non-Accomplice Vendor Fraud: Operates through deliberate overpayments or duplicate payments, with perpetrators intercepting subsequent refunds. This scheme requires no vendor participation or awareness.
- Documented Case Study: Veronica, an accounts payable employee, systematically processed invoices twice before intercepting supplier refund checks. Her external accomplice deposited these checks using forged endorsement stamps. This sophisticated operation resulted in more than $250,000 stolen over less than two years.
- Detection Challenges: These schemes prove particularly difficult to identify because they exploit legitimate vendor relationships and normal refund processes.
Personal Purchases: Converting Company Assets for Individual Benefit
- Employee Exploitation: Involves systematic charging of personal expenses through business accounts, representing both tax evasion and fraudulent activity.
- Common Manifestations:
Direct Cash Withdrawal: Using company debit cards for personal purchases.
Bill Payment Fraud: Redirecting company funds toward personal obligations.
Cash Diversion: Taking cash payments intended for business operations.
Real Estate Acquisition: Using company funds for personal property purchases.
- Regulatory Consequences: Even seemingly minor fraudulent expenses of $500 can trigger extensive IRS scrutiny, creating significant organizational disruption and investigative burden.
- Pass-Through Billing: Healthcare Industry Exploitation
- Third-Party Service Fraud: Involves fraudulently billing for services performed by other entities. This scheme achieved prominence in healthcare fraud cases, including a $1.4 billion fraud involving rural hospitals.
- Sophisticated Arrangements: Perpetrators create false appearances that healthcare facilities performed services actually conducted elsewhere. These schemes frequently target vulnerable patients acquired through recruiter kickbacks.
Duplicate Invoicing: Systematic Payment Multiplication
- Processing Exploitation: Organizations typically experience approximately six duplicate invoices monthly, averaging $2,034 each—creating potential monthly losses of $12,000 if undetected.
- Manifestation Patterns:
- Identical Duplication: Exact copies of previously processed invoices.
- Modified Duplicates: Invoices with slight variations from originals.
- Multi-Channel Submission: Bills submitted simultaneously through different processing channels.
- Financial Impact: This scheme strains cash flow, wastes investigative resources, and distorts financial record accuracy.
Ghost Vendor Payments: Fictitious Supplier Networks
- Fabricated Supplier Schemes: Involve creating fictitious suppliers within payment systems to submit fraudulent invoices for non-existent goods or services. These schemes require extensive planning, often involving document forgery and identity impersonation.
- Warning Indicators: Unusual vendor names, post office box addresses instead of physical locations, and frequent invoice amount changes signal potential ghost vendor activity. These frauds typically bypass traditional verification because ghost vendors appear legitimate within organizational systems.
Credit Card Misuse: Corporate Card Exploitation
- Unauthorized Personal Usage: Involves employees making personal purchases through corporate credit cards. While using company cards for personal items isn’t inherently illegal, failing to report such usage promptly crosses into fraud territory.
- Legal Ramifications: This represents common embezzlement that can trigger serious legal consequences depending on misappropriated amounts. Credit card misuse directly impacts company finances while potentially damaging credit eligibility and stakeholder confidence.
Bid Rigging and Kickbacks: Contract Competition Manipulation
- Competitive Process Fraud: Involves competitors agreeing on contract winners, eliminating genuine competition through four primary schemes:
-
- Bid Suppression: Competitors agree to withdraw bids or refrain from bidding.
- Complementary Bidding: Submitting intentionally high or non-compliant proposals.
- Bid Rotation: Taking turns being the lowest bidder across different contracts.
- Market Allocation: Dividing customers or geographic territories among conspirators.
- Subcontracting Arrangements: Often accompany these schemes, with losing bidders receiving contracts from winners. Suspicious indicators include identical bid amounts, significant gaps between winning and losing proposals, and physical evidence like submissions with identical handwriting.
- Detection Imperative: Understanding these sophisticated techniques empowers organizations to implement targeted countermeasures before schemes inflict substantial financial damage. Each represents a systematic attack on internal controls that requires comprehensive fraud prevention strategies.
Corporate Case Studies: The Devastating Reality of Billing Scheme Fraud
- Real-world billing scheme cases demonstrate how sophisticated deception destroys organizational assets and exposes the critical importance of internal control systems. These documented failures reveal patterns that every organization must recognize to protect against similar devastating losses.
Manufacturing Sector Fraud: $1.5 Million Vendor Collusion Scheme
- XYZ Manufacturing Company’s experience with Global Metals Ltd. illustrates how vendor relationships can mask sophisticated fraud operations. The energy company awarded a contract for rare earth metals that appeared legitimate but evolved into a 1.5 million loss through coordinated deception.
Dual-Mechanism Fraud Operation:
- The scheme operated through two interconnected approaches that exploited systemic weaknesses:
-
- False Invoice Submissions: Global Metals systematically submitted invoices for products that remained partially delivered or never shipped, targeting XYZ’s accounting system that lacked quantity verification controls.
-
- Internal Procurement Manipulation: A procurement department employee deliberately altered purchase orders and delivery documentation, enabling fraudulent invoices to bypass detection systems in exchange for personal kickbacks.
- Broader Industry Impact: This case exemplifies vendor fraud patterns that combine external and internal elements. The Association of Certified Fraud Examiners documents that organizations lose 5% of annual revenue to fraud, with potential worldwide losses exceeding $5 trillion annually.
Financial Institution Vulnerability: Dormant Account Exploitation
- Dormant vendor accounts create particularly insidious risks for financial institutions and businesses. These seemingly inactive accounts function as financial “Trojan horses”—appearing benign while harboring potential for catastrophic fraud activation.
- Exploitation Methods:
- Fraudsters manipulate dormant accounts through multiple sophisticated approaches:
-
- Channeling stolen funds through inactive accounts
- Misrepresenting organizational financial positions
- Building foundations for larger “bust-out” fraud schemes
- Dangerous Misconceptions: Organizations often develop false confidence in dormant accounts based solely on their longevity, despite lacking transaction history verification. This creates perverse incentives for criminals to establish multiple accounts specifically for future fraudulent exploitation.
- Recent Breach Example: Tangerine’s February 2024 data breach traced to contractor login credentials demonstrates these vulnerabilities. The credentials remained active on a legacy database scheduled for retirement, exposing personal data for more than 230,000 customers.
Retail Crime Network: $19 Million Multi-Channel Operation
Philadelphia pawn shop owners Larry and Nathaniel Leonard operated a sophisticated criminal enterprise that demonstrates how billing fraud intersects with broader criminal activities. The cousins controlled three pawn shops while purchasing stolen retail merchandise from professional thieves and reselling through their eBay operation.
Criminal Operation Structure:
The enterprise employed systematic methods for maximizing stolen merchandise value:
- Purchasing inventory from professional thieves classified as “boosters” and “mooks”
- Transferring stolen goods between multiple pawn shop locations
- Generating over $19 million in stolen merchandise sales via eBay between 2019 and 2023
- Money Laundering Component: Larry Leonard faced additional charges for using illegal sale proceeds to eliminate more than $120,000 in credit card obligations between December 2022 and April 2023.
- Retail Target Scope: The operation specifically targeted major retailers including Home Depot, Lowe’s, Target, Walmart, Best Buy, CVS, and others.
Healthcare Billing Fraud: $336 Million Insurance Deception
- Healthcare sectors present unique vulnerabilities to billing fraud schemes. A 2022 case involving a New York medical biller demonstrates the scale of potential losses through systematic insurance company deception.
- Fraudulent Claim Manipulation: The perpetrator submitted false claims for procedures that exceeded the severity of actual treatments or represented completely fabricated services. The scheme involved impersonating patients during thousands of calls to insurance companies, convincing them to reverse previously denied claims.
- Industry-Wide Implications: These healthcare fraud cases reveal how billing schemes adapt to industry-specific vulnerabilities, requiring sector-tailored prevention strategies and enhanced verification protocols.
- Systematic Pattern Recognition: Each documented case reveals common elements: exploitation of weak verification systems, internal collusion opportunities, and the intersection of billing fraud with broader criminal enterprises. Organizations that understand these patterns can implement targeted internal controls before similar schemes devastate their operations.
Red Flags and Behavioral Indicators: Detecting Billing Fraud Before Catastrophic Losses
- Detecting billing schemes requires systematic attention to specific warning signs that consistently appear before major fraud discoveries. These red flags provide essential early detection capabilities that enable organizations to prevent significant losses and implement appropriate countermeasures.
Suspicious Vendor Characteristics and Documentation Irregularities
- Questionable vendor profiles often constitute the primary indication of potential billing fraud. Perpetrators typically establish fictitious companies that appear legitimate initially but contain detectable irregularities that careful analysis can reveal.
- Critical vendor warning signs include:
- Vendors utilizing post office box addresses rather than physical business locations
- Suppliers sharing residential addresses or identical addresses with other vendors
- Vendors unknown to staff or managed exclusively by a single employee
- Suppliers with names closely resembling legitimate vendors but containing slight variations
- Previously unknown vendors appearing suddenly without proper verification processes
- Vendors lacking contracts, references, or documented transaction history
- Invoice documentation examination reveals additional fraud indicators. Soiled or incomplete invoices, unfolded invoices suggesting they were never mailed, and invoices from different suppliers printed on identical stationery signal potential fraudulent activity.
Invoice Pattern Anomalies and Amount Manipulation
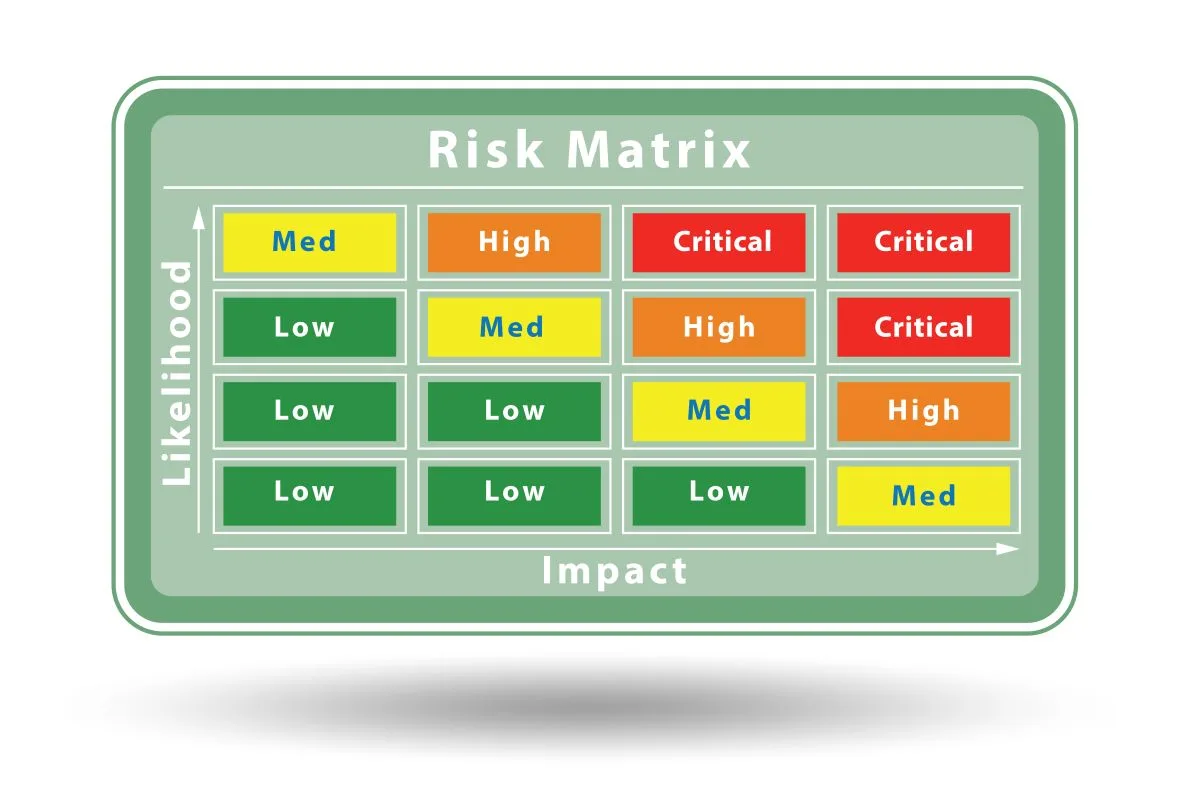
- Invoice irregularities represent another critical category of fraud detection indicators. Perpetrators frequently manipulate amounts or submit strategically sized invoices to circumvent detection thresholds and approval processes.
Suspicious invoice patterns warrant immediate investigation:
- Round number invoices (such as exactly $5,000.00 rather than $5,123.78) frequently indicate fabricated charges. Invoice splitting tactics involve multiple small-value invoices positioned just below approval thresholds to avoid triggering multi-level reviews.
- Vague service descriptions or invoices lacking specific details about delivered products should raise concerns, as legitimate vendors typically provide comprehensive information about deliverables and timing.
- Unexplained changes in invoice frequency or amounts from particular vendors without clear business justification require thorough investigation.
Employee Behavioral Red Flags and Lifestyle Indicators
- Employee behavior patterns provide crucial insights into potential fraudulent involvement. The Association of Certified Fraud Examiners reports that 41% of fraud cases involve perpetrators living beyond their apparent means.
- Key behavioral indicators include:
-
- Employees displaying expensive purchases inconsistent with their compensation levels
- Staff experiencing financial difficulties (present in 29% of fraud cases)
- Employees refusing to delegate financial functions or share client relationships
- Staff resisting vacation time or training others in their responsibilities
- Employees exhibiting personality changes or demonstrating poor financial management
- Additional risk factors include employees experiencing divorce or family problems (14% of cases) and those expressing job dissatisfaction (9% of cases), which may elevate fraud risk.
Vendor-Employee Connections and Collusion Patterns
- Connections between employees and vendors represent critical fraud indicators requiring immediate attention. Research demonstrates that approximately 40% of occupational fraud cases involve employee collusion.
- Suspicious connection patterns include:
-
- Information overlap between vendor contact details and employee information demands immediate investigation. Address matching between vendors and employees or their relatives strongly suggests potential fraud schemes. Identical banking arrangements where multiple vendors utilize the same bank accounts indicate possible money laundering or fictitious vendor operations.
-
- Unusually close vendor relationships appeared in 20% of studied fraud cases. This frequently manifests as employees who refuse to work with suppliers other than their preferred vendors or who maintain suspiciously intimate business relationships with certain companies.
-
- Early detection of these warning signs enables organizations to investigate potential fraud before substantial losses occur. Understanding these behavioral indicators and documentation red flags empowers management to implement targeted internal controls and prevent devastating financial consequences.
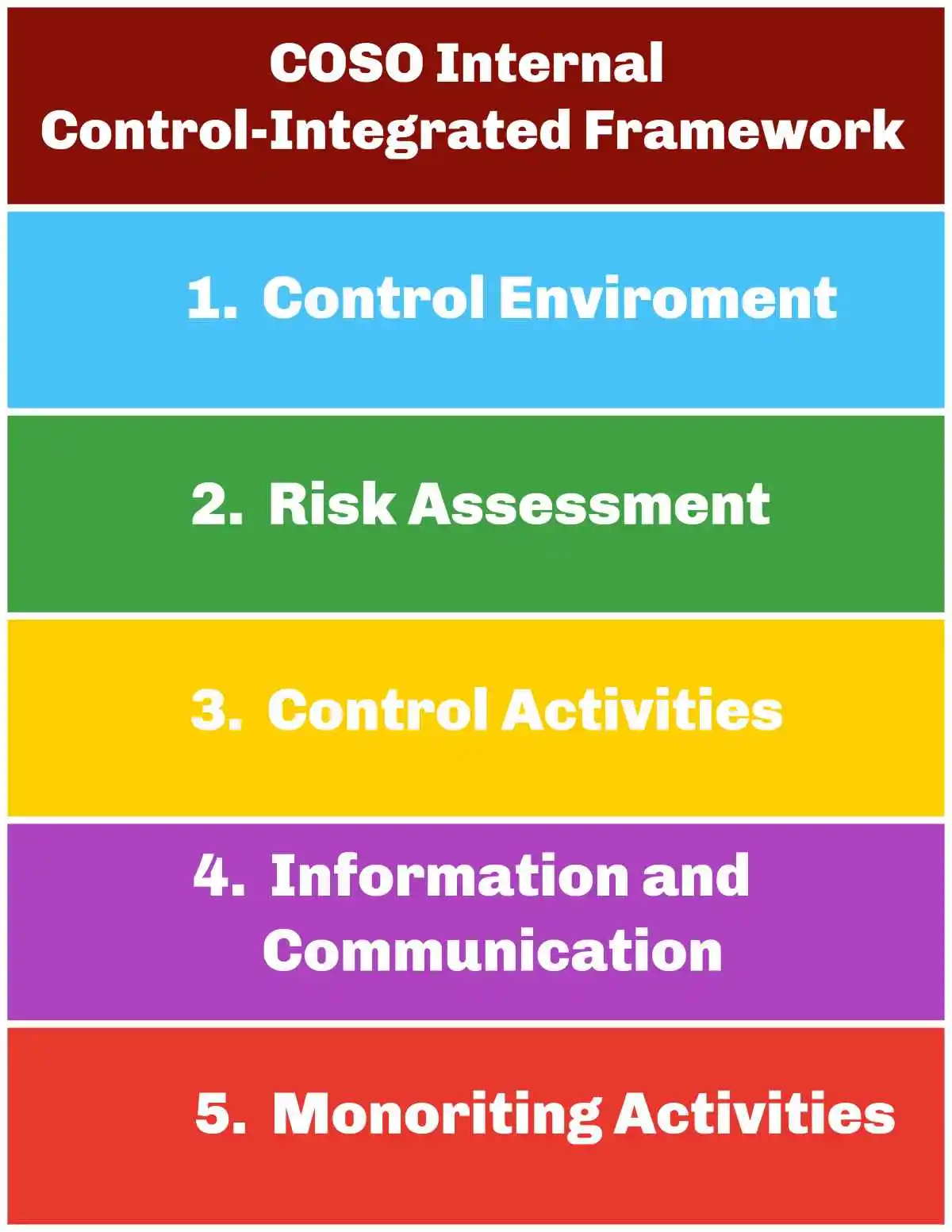
Internal Controls to Prevent Billing Schemes
- Robust Defense Systems: Implementing comprehensive internal controls forms the cornerstone of effectivebilling scheme prevention and accounting fraud protection. These multi-layered systems create essential barriers that safeguard organizational assets from misappropriation attempts and financial deception.
Segregation of Duties in AP and Procurement
- Minimum Standards: No individual should possess authority to initiate, approve, record, and reconcile transactions within the same process. Organizations require at minimum three separate employees to handle:
-
- Product purchasing and ordering
- Receipt confirmation and verification
- Invoice review and approval
- System data entry processes
- Payment processing activities
- Check signing authority
- Compensating Controls: Organizations with limited staffing must implement enhanced supervisory reviews and additional oversight mechanisms to offset segregation limitations.
Three-Way Matching: PO, Invoice, Receiving Report
- Verification Process: Three-way matching creates a powerful detection mechanism that identifies fraudulent disbursements and unauthorized transactions before payment occurs.
- Document Cross-Reference System: This verification process requires simultaneous review of three critical documents:
-
- Purchase Order – Establishes agreed quantities, specifications, and pricing terms
- Delivery Receipt – Confirms actual receipt of goods or services
- Supplier Invoice – Documents payment obligations and terms
- Critical Verification Points: Accounts payable personnel must confirm these essential elements:
- Purchase order accuracy including amounts, vendor information, and general ledger coding
- Quantity alignment between ordered and received merchandise
- Price verification against authorized purchase order terms
- Enhanced Protection: Research demonstrates that small businesses experience billing fraud twice as frequently as larger organizations, making three-way matching particularly valuable for fraud prevention.
Vendor Master File Review and Cleanup
- System Integrity: Maintaining accurate vendor master files proves essential for preventing duplicate payments, ensuring data accuracy, and deterring fraudulent vendor schemes.
- Essential Maintenance Activities:
-
- Elimination of duplicate vendor entries that create payment vulnerabilities
- Verification of contact information including addresses, phone numbers, and email accounts
- Confirmation of banking details, payment terms, and tax identification numbers
- IRS verification of tax identification number accuracy against vendor names
- Archive removal of suppliers inactive for 15-18 months
- Access Controls: Vendor master file access should remain restricted to authorized personnel responsible for new account creation and existing account updates. This segregation creates additional protection against errors and fraudulent manipulation.
Bank Reconciliation and Audit Trails
- Detective Controls: Bank reconciliation functions as a systematic safeguard that identifies errors, discrepancies, and fraudulent activities before they cause substantial organizational damage.
- Independence Requirements: Personnel assigned to bank reconciliation responsibilities must remain separate from:
-
- Bank deposit handling and processing
- Accounts payable and payroll check management
- Electronic fund transfer authorization
- Bank account signatory responsibilities
- Secondary Review Protection: Independent reconciliation reviews create additional security layers. Reviewers require access to original bank statements or view-only online statement access. This secondary verification becomes particularly critical for smaller organizations with limited duty segregation capabilities and is a vital component of robust corporate governance frameworks and strong internal controls to stay in regulatory compliance and avoid securities litigation.
- Proactive Detection: Regular reconciliation enables identification of unauthorized withdrawals, duplicate payments, and forged instruments before significant losses occur. Consistent reconciliation practices establish a culture of financial discipline that naturally deters internal fraud attempts.
Corporate Governance and Whistleblower Protections: Essential Defenses Against Billing Fraud
- Corporate governance: Establishes the fundamental framework that strengthens internal controls and creates accountability mechanisms essential for combating billing schemes and accounting fraud. Effective governance structures provide oversight capabilities that monitor financial processes while fostering ethical conduct throughout the organization.
Whistleblower Hotlines: Critical Detection Mechanisms
Whistleblower hotlines serve as essential early-warning systems against billing fraud schemes. Research demonstrates that 42% of all fraud cases are detected through tips, with over half originating from employees. Organizations lacking established reporting mechanisms experience fraud losses approximately twice as high as those with comprehensive whistleblower programs. Companies must implement robust corporate governance frameworks and strong internal controls to stay in regulatory compliance and avoid securities litigation.
- Essential Implementation Components:
- Awareness Programs: Employees must receive thorough training about reporting mechanisms through orientation processes and ongoing education initiatives.
- Accessibility Standards: Systems must operate continuously from any location, ideally supporting multiple languages to accommodate diverse workforces.
- Multiple Reporting Channels: Organizations should offer various communication methods including email, web portals, and telephone systems to maximize utilization.
- Anti-Retaliation Policies: Strict protections for whistleblowers prove essential for encouraging the reporting of suspicious activities.
- Strategic Communication: Organizations must establish clear guidelines defining reportable events while providing comprehensive risk-awareness training that supports confidential reporting. These measures create organizational cultures where ethical behavior becomes the established standard.
Board Oversight and Audit Committee Responsibilities
- Audit committees: Function as pivotal defenders against billing schemes through comprehensive oversight of financial reporting, internal controls, risk management, and compliance frameworks. Their fundamental responsibilities include:
-
- Fraud Prevention Systems: Ensuring appropriate anti-fraud controls and detection programs operate effectively throughout the organization.
-
- Incident Response Protocols: Taking immediate corrective action when billing fraud or other misconduct is discovered.
-
- Ethics Program Implementation: Establishing comprehensive ethics and compliance initiatives that prevent fraudulent activities.
-
- Reporting System Oversight: Maintaining effective hotlines and other communication channels for fraud detection.
-
- The Fraud Triangle Framework: Effective audit committees recognize the three critical fraud risk factors that typically enable billing schemes: incentive or pressure, opportunity, and rationalization. Understanding these elements allows committees to fulfill their oversight obligations by addressing root causes rather than symptoms.
Ethics Training and Comprehensive Fraud Awareness Programs
- Ethics training programs: Transform employees into front-line defenders against billing schemes and accounting fraud. Comprehensive programs must focus on specific objectives:
-
- Organization-Wide Fraud Awareness: Developing deep understanding of billing fraud tactics and their devastating financial consequences throughout all organizational levels.
-
- Ethical Culture Development: Instilling strong cultural foundations emphasizing integrity, honesty, and transparent financial practices.
-
- Customized Content Delivery: Tailoring training materials to address specific regulatory compliance requirements and unique business unit vulnerabilities.
-
- Clear Reporting Mechanisms: Establishing accessible communication channels that encourage prompt reporting of suspicious activities.
-
- Program Implementation Standards: Training initiatives must incorporate interactive learning modules, continuous reinforcement through regular updates, and visible leadership participation demonstrating organizational commitment. Organizations failing to provide comprehensive fraud awareness training experience losses nearly twice as substantial as those maintaining robust educational programs.
-
- Effectiveness Measurement: Regular assessment of program impact through employee feedback, incident reporting rates, and detection statistics ensures continuous improvement. When employees understand their essential role in fraud prevention, they become invaluable assets protecting organizational resources from billing schemes and other fraudulent activities.
-
- Governance Integration: These governance mechanisms must operate as integrated systems rather than isolated initiatives. Effective corporate governance creates multiple layers of protection that make billing fraud schemes significantly more difficult to execute and conceal, ultimately safeguarding organizational assets from the devastating financial losses associated with asset misappropriation.
Regulatory Compliance and Legal Implications: The Enforcement Framework
Regulatory frameworks establish critical safeguards against billing schemes and accounting fraud, creating substantial legal consequences that extend far beyond simple financial penalties. Organizations and executives involved in financial misconduct face increasingly severe enforcement actions designed to protect market integrity and investor confidence. Companies must implement robust corporate governance frameworks and strong internal controls to stay in regulatory compliance and avoid securities litigation.
Securities Class Actions and Litigation Exposure
- Securities class action lawsuits represent devastating litigation risks for companies confronting allegations of accounting fraud. These lawsuits typically emerge following negative corporate disclosures accompanied by substantial stock price declines. Plaintiffs’ attorneys maintain significant control over case direction, determining which actions to pursue and litigation strategies.
- Financial Consequences: Prove severe as plaintiffs’ lawyers receive approximately 40% of any settlement or judgment, plus additional costs incurred during securities litigation. The substantial expense of defending these suits often compels companies to settle quickly, regardless of merit.
- Legislative Response: Congress enacted the Private Securities Litigation Reform Act (PSLRA) in 1995 to combat frivolous “strike” securities class action lawsuits by establishing specific pleading standards that plaintiffs must satisfy. These requirements help filter legitimate claims from opportunistic litigation.
THE SECURITIES LITIGATION PROCESS
| Filing the Complaint | A lead plaintiff files a lawsuit on behalf of similarly affected shareholders, detailing the allegations against the company. |
| Motion to Dismiss | Defendants typically file a motion to dismiss, arguing that the complaint lacks sufficient claims. |
| Discovery | If the motion to dismiss is denied, both parties gather evidence, documents, emails, and witness testimonies. This phase can be extensive. |
| Motion for Class Certification | Plaintiffs request that the court to certify the lawsuit as a class action. The court assesses factors like the number of plaintiffs, commonality of claims, typicality of claims, and the adequacy of the proposed class representation. |
| Summary Judgment and Trial | Once the class is certified, the parties may file motions for summary judgment. If the case is not settled, it proceeds to trial, which is rare for securities class actions. |
| Settlement Negotiations and Approval | Most cases are resolved through settlements, negotiated between the parties, often with the help of a mediator. The court must review and grant preliminary approval to ensure the settlement is fair, adequate, and reasonable. |
| Class Notice | If the court grants preliminary approval, notice of the settlement is sent to all class members, often by mail, informing them about the terms and how to file a claim. |
| Final Approval Hearing | The court conducts a final hearing to review any objections and grant final approval of the settlement. |
| Claims Administration and Distribution | A court-appointed claims administrator manages the process of sending notices, processing claims from eligible class members, and distributing the settlement funds. The distribution is typically on a pro-rata basis based on recognized losses. |
PRE- AND POST-PSLRA STANDARDS FOR SECURITIES FRAUD LITIGATION AND SECURITIES CLASS ACTIONS
|
Feature |
Pre-PSLRA Standard |
Post-PSLRA Standard |
|
Motion to dismiss |
Based on “notice pleading” (Federal Rule of Civil Procedure 8(a)), making it easier for plaintiffs to survive motions to dismiss. This often led to settlements to avoid costly litigation. |
Requires satisfying PSLRA’s heightened pleading standards and the “plausibility” standard from Twombly and Iqbal. Failure to plead with particularity on any element can result in dismissal. |
|
Pleading |
“Notice pleading” was generally sufficient, though fraud claims under Federal Rule of Civil Procedure 9(b) required particularity for the circumstances of fraud, but intent could be alleged generally. |
Each misleading statement must be stated with particularity, explaining why it was misleading. Facts supporting beliefs in claims based on “information and belief” must also be stated with particularity. |
|
Scienter |
Pleaded broadly; the “motive and opportunity” test was often sufficient to infer intent. |
Requires alleging facts creating a “strong inference” of fraudulent intent, which must be at least as compelling as any opposing inference of non-fraudulent intent, as clarified in Tellabs, Inc. v. Makor Issues & Rights, Ltd.. |
|
Loss causation |
Not a significant pleading hurdle, often assumed if a plaintiff bought at an inflated price. |
Requires pleading facts showing the fraud caused the economic loss, often by linking a corrective disclosure to a stock price drop. Dura Pharmaceuticals, Inc. v. Broudo affirmed this. |
|
Discovery |
Could proceed while a motion to dismiss was pending. |
Automatically stayed during a motion to dismiss. |
|
Safe harbor for forward-looking statements |
No statutory protection. |
Protects certain forward-looking statements if accompanied by “meaningful cautionary statements”. |
|
Lead plaintiff selection |
Often the first investor to file. |
Court selects based on a “rebuttable presumption” that the investor with the largest financial interest is the most adequate. |
|
Liability standard |
For non-knowing violations, liability was joint and several. |
For non-knowing violations, liability is proportionate; joint and several liability applies only if a jury finds knowing violation. |
|
Mandatory sanctions |
Available under Federal Rule of Civil Procedure 11, but judges were often reluctant to impose them. |
Requires judges to review for abusive conduct |
Sarbanes-Oxley Compliance: Executive Accountability Framework Along with Securities Litigation.
- The Sarbanes-Oxley Act of 2002 following the collapse of Enron and WorldCom, fundamentally transformed financial reporting regulatory compliance requirements. The Act mandates comprehensive reporting and control structures:
- Critical SOX Requirements:
-
- Annual financial reports must include comprehensive Internal Controls assessments
- Accurate financial data supported by robust safeguarding controls
- Timely year-end financial disclosure reports
- Whistleblower protection for employees reporting corporate fraud
- Executive Responsibility: Section 302 places direct accountability on CEOs and CFOs for financial report accuracy. Section 404 requires annual reports include Internal Control assessments outlining management’s responsibility for maintaining adequate control structures.
- Criminal Penalties: Non-compliance triggers severe consequences including fines up to $5 million and imprisonment for up to 20 years for executives who knowingly certify false financial reports.
Suspicious Activity Reporting: Federal Compliance Obligations and Risk of Securities Class Actions
- Reporting Thresholds: Certain businesses must report suspicious activity involving transactions of $2,000 or more. Organizations must file Suspicious Activity Reports (SARs) within 30 calendar days of discovering suspicious transactions.
- Documentation Requirements: Supporting documentation related to SARs must be maintained for 5 years. Federal law provides civil liability protection for individuals who report suspicious activities in good faith.
- Structuring Violations: Deliberately designing transactions to evade reporting requirements constitutes a federal crime requiring immediate reporting. These violations demonstrate how billing fraud schemes can escalate into serious federal offenses with substantial criminal penalties.
- Comprehensive Protection: Organizations that maintain robust regulatory compliance programs significantly reduce their exposure to both civil litigation and criminal prosecution while protecting stakeholder interests.
Advanced Technology Solutions: Defending Against Evolving Billing Fraud and Avoiding Securities Litigation
- Technological Innovation: Organizations now deploy sophisticated automated fraud prevention systems that provide unprecedented protection against evolving financial threats that traditional detection methods cannot identify. This technology can also help companies implement robust corporate governance frameworks and strong internal controls.
- AI-Powered Detection Systems: The deployment of artificial intelligence fundamentally transforms how organizations identify accounting fraud patterns that escape human detection capabilities.
AI-Based Fraud Detection: Real-Time Protection Against Sophisticated Schemes
- Artificial Intelligence Detection: AI-powered detection systems continuously analyze invoice patterns, instantly flagging duplicate payments and unauthorized transactions. These advanced systems identify anomalies significantly faster than traditional reactive approaches. It also helps companies implement robust corporate governance frameworks and strong internal controls.
- Enhanced Vendor Verification: AI systems assess payment details, contract modifications, and vendor financial stability. This proactive approach reduces fraud risk before financial damage occurs. Agentic AI represents the next technological evolution—systems that observe environments, learn from patterns, and initiate independent protective decisions.
- Critical Advantages: AI-based fraud detection delivers measurable improvements in organizational protection:
-
- False Positive Reduction: Reduction in false positives by up to 90% through sophisticated evaluation of vendor behavior patterns and transaction history.
- Early Intervention Capabilities: Systems intervene earlier in workflows to block unverified vendors and pause suspicious invoices before payment processing.
- Self-Learning Enhancement: Advanced algorithms refine risk assessment models based on outcomes and feedback, creating increasingly accurate detection capabilities.
Benford’s Law: Mathematical Analysis for Fraud Detection
- Mathematical Detection Methods: Benford’s Law provides a powerful analytical tool for identifying numerical manipulation within accounting records. This mathematical principle demonstrates that naturally occurring datasets exhibit predictable digit distribution patterns—with the numeral 1 appearing as the first digit approximately 30.1% of the time.
- Audit Applications: Forensic accounting professionals apply Benford’s Law to examine journal entries for unusual numeric patterns that indicate potential manipulation. When fraudsters manually insert fabricated numbers into naturally occurring datasets, these entries typically fail to match expected mathematical patterns.
Continuous Monitoring Systems: Proactive Fraud Prevention
- Automated Analytics: Continuous monitoring represents a significant advancement in procurement fraud prevention through automated analytics that rapidly identify risks and errors within transactional data. Predefined fraud scenarios combined with proven detection models uncover unusual employee behavior, duplicate invoices, and contract discrepancies.
- Predictive Analytics Evolution: These systems will advance substantially over the next two to three years through integration with big data platforms and deep learning technologies. Advanced detection systems process vast quantities of transactional information at unprecedented speeds, enabling near-zero tolerance for fraudulent activities.
- Future Protection Framework: The technological evolution points toward proactive, transparent, and stakeholder-focused fraud prevention systems. Organizations that implement these advanced detection technologies create multiple layers of protection against the sophisticated billing fraud schemes that continue to evolve and threaten organizational assets.
- Investment Protection: The cost of implementing these technological solutions proves substantially lower than the devastating losses that result from undetected billing scheme fraud. Organizations must recognize that fraudsters continuously adapt their techniques, making technological advancement essential for maintaining effective protection against financial deception.
Organizational Protection Against Billing Schemes: Essential Defense Strategies
- Billing scheme threats continue to devastate organizations across all sectors, generating median losses of $100,000 per occurrence. This analysis has revealed the sophisticated mechanisms underlying billing fraud, documented real-world cases, and established proven countermeasures that organizations must deploy to protect their assets. Companies must implement robust corporate governance frameworks and strong internal controls.
- Multi-Layered Defense Requirements: Organizations face a critical reality—fraud prevention demands comprehensive, integrated approaches that address multiple vulnerability points simultaneously. The most effective protection strategies encompass:
-
- Segregation of duties that prevents single-point-of-failure scenarios in accounts payable and procurement functions. One of the bedrocks of good corporate governance and strong internal controls.
-
- Vendor master file maintenance through regular reviews and systematic cleanup procedures that eliminate dormant account risks
-
- Three-way matching verification processes that cross-reference purchase orders, invoices, and receiving reports before payment authorization
-
- Whistleblower programs that create reporting mechanisms for suspicious activities while protecting employees from retaliation
-
- Fraud awareness training that empowers staff to recognize warning signs and respond appropriately to potential threats
-
- Early Detection Systems: Red flags such as unusual vendor characteristics, invoice irregularities, and employee behavioral changes provide crucial early warning indicators. Organizations that maintain vigilant monitoring of these patterns can intervene before substantial losses occur, protecting both financial assets and organizational reputation.
-
- Legal and Regulatory Compliance: Regulatory compliance requirements under Sarbanes-Oxley, securities class action awareness, and suspicious activity reporting obligations create additional protective layers. Understanding these legal frameworks helps organizations meet compliance requirements while strengthening their overall fraud prevention posture.
-
- Advanced Technology Integration: AI-based detection systems, Benford’s Law analysis, and continuous monitoring represent the next generation of fraud detection capabilities. These technological solutions identify suspicious patterns that traditional manual reviews cannot detect, enabling organizations to stay ahead of evolving billing fraud tactics
-
- Adaptive Vigilance Required: Fraudulent schemes constantly evolve as perpetrators develop new methods to exploit organizational vulnerabilities. Organizations must maintain ongoing assessment and enhancement of protective measures to counter these adaptive threats. The schemes that prove successful today will likely evolve tomorrow, requiring continuous improvement in detection and prevention strategies.
-
- Comprehensive Protection Strategy: Proactive leadership, combined with knowledgeable employees and technological solutions, creates formidable defenses against billing schemes and asset misappropriation. This integrated approach protects financial resources while preserving stakeholder trust and organizational integrity within increasingly complex business environments.
-
- Future Vigilance: The battle against billing fraud requires sustained commitment from all organizational levels. Companies that prioritize transparent financial reporting, implement robust internal controls, and foster ethical business cultures will be best positioned to protect their assets from the devastating consequences of accounting fraud.
Key Takeaways
Understanding billing schemes and implementing and is strong corporate governance and robust internal controls. is crucial for protecting your organization from devastating financial losses that average $100,000 per incident.
• Billing schemes account for 22% of asset misappropriation cases, making them one of the most common and costly forms of internal fraud facing businesses today.
• Implement three-way matching processes comparing purchase orders, invoices, and receiving reports to catch fraudulent transactions before payment occurs and is good corporate governance and shows strong internal controls.
• Watch for red flags like unusual vendor names, PO box addresses, and employees living beyond their means – these behavioral indicators often signal potential fraud activity.
• Segregate duties across purchasing, approval, and payment functions to prevent any single employee from controlling the entire billing process and committing fraud.
• Deploy AI-powered fraud detection systems and continuous monitoring to identify suspicious patterns and anomalies that traditional manual reviews might miss.
• Establish whistleblower hotlines and ethics training programs – organizations without reporting mechanisms experience fraud losses including fake invoices, or another fraud scheme twice as high as those with established systems.
The future of fraud prevention lies in combining strong internal controls with advanced technology. Organizations that proactively implement comprehensive anti-fraud measures, maintain vigilant oversight, and foster ethical cultures will be best positioned to protect their assets from evolving billing scheme tactics in 2025 and beyond.
FAQs
Q1. What are some common red flags that may indicate billing fraud and not being in regulatory complaince? Common red flags include unusual vendor names or PO box addresses, frequent invoice amount changes, employees living beyond their means, and mismatches between vendor and employee information. Vigilant monitoring of these indicators allows for prompt intervention.
Q2. How can organizations implement effective internal controls and corporate governance to prevent billing schemes and maintain regulatory compliance? Organizations can implement segregation of duties in accounts payable and procurement, use three-way matching of purchase orders, invoices, and receiving reports, regularly review and clean up vendor master files, and conduct thorough bank reconciliations with clear audit trails.
Q3. What role does technology play in detecting and preventing billing fraud and maintain regulatory compliance? Technology plays a crucial role through AI-based fraud detection systems, AP automation, and continuous monitoring. These advanced tools can identify suspicious patterns, flag anomalies, and detect fraud much faster than traditional manual methods.
Q4. How important are whistleblower policies in combating billing fraud and maintain regulatory compliance? Whistleblower policies are critical. Organizations with established reporting mechanisms experience fraud losses about half as large as those without such systems. Implementing a whistleblower hotline and fostering a culture that encourages reporting can significantly enhance fraud prevention efforts.
Q5. What are the potential consequences for companies that fail to prevent billing fraud? Consequences can be severe, including substantial financial losses (median of $100,000 per occurrence), damage to reputation, regulatory penalties, and potential legal action. For publicly traded companies, non-compliance with regulations like Sarbanes-Oxley can result in hefty fines and even imprisonment for executives.