Introduction to Control Implementation
- Control implementation failures triggered a significant amount all workplace fraud cases in 2020, representing billions in corporate losses and countless securities class action lawsuits filed by investors seeking recovery for fraud-related damages.
- Internal controls serve as the primary defense mechanism against accounting fraud, financial statement manipulation, and the devastating securities litigation that inevitably follows corporate misconduct. These systematic safeguards protect organizational assets, ensure accurate financial reporting, and maintain regulatory compliance with federal securities laws—functions that cannot be treated as optional in today’s enforcement environment. Employee misconduct accounts for 70% of corporate breaches, underscoring why robust internal control systems represent a fundamental business necessity rather than merely a compliance exercise.
- Preventative controls and detective controls work together to create multiple layers of protection against corporate fraud. Preventative controls identify and address potential problems before they escalate into serious legal issues, effectively stopping fraudulent activities at their source before they can trigger corrective disclosuresand subsequent investor losses. Organizations with effective internal controls demonstrate their commitment to corporate governance principles while supporting sustainable growth through transparent and accountable operations.
- Risk assessment processes require annual revision to address evolving business conditions and emerging fraud schemes. Companies operating in dynamic markets face increased scrutiny from regulators and investors, making adaptive internal controls essential for maintaining stakeholder confidence and avoiding costly enforcement actions. Advanced technologies now enable more sophisticated control monitoring and real-time fraud detection capabilities that strengthen traditional control frameworks.
- This systematic eight-step process provides organizations with practical strategies for implementing robust internal controls that protect against fraud, ensure regulatory compliance, and mitigate the risk of securities class action litigation. Each step addresses critical vulnerabilities that have historically led to corporate scandals and massive investor settlements.
Step 1: Establish a Strong Control Environment
Control environment establishes the foundational framework that determines whether other internal controlcomponents can function effectively in preventing accounting fraud and securities litigation. This critical foundation shapes organizational attitude and management commitment to regulatory compliance, directly influencing whether companies become targets of SEC enforcement actions or costly securities class action lawsuits.
1. Define ethical values and tone at the top
- Tone at the top emerged as a crucial governance principle following devastating corporate scandals including Enron and WorldCom, which demonstrated how leadership failures cascade into massive securities fraud cases and billions in investor losses. Board of directors and senior management must establish unambiguous standards regarding ethical conduct and internal control effectiveness to prevent the type of misconduct that triggers corrective disclosures and subsequent litigation.
- Strong ethical foundations require specific implementation measures:
-
- Code of conduct development with clear organizational values and compliance expectations
-
- Management demonstration of integrity through consistent actions rather than superficial policy statements
-
- Regular ethical discussions that address real-world compliance dilemmas employees face
-
- Executive accountability where leaders follow identical standards applied throughout the organization
- Organizations lacking established ethical frameworks consistently fail to achieve operational objectives or maintain accurate financial reporting. When senior executives demonstrate accountability through their daily decisions, they create the cultural foundation necessary to prevent corporate governance failures and associated securities litigation.
2. Clarify roles and responsibilities
- Clear accountability structures eliminate the ambiguity that enables fraudulent activities to flourish undetected. Well-defined responsibilities create ownership expectations that serve as both preventive measures and detection mechanisms when accounting irregularities occur.
- Effective role definition encompasses critical elements:
-
- Comprehensive job descriptions specifying duties that support internal control objectives
-
- Measurable performance indicators directly tied to compliance and fraud prevention goals
-
- Clear reporting structures that facilitate prompt escalation of potential violations
-
- Decision-making authority limitations that prevent single individuals from circumventing controls
- Organizational structures must explicitly address authority restrictions and responsibility assignments essential for risk mitigation. These frameworks ensure critical functions receive appropriate oversight while preventing conflicts of interest that historically contribute to corporate scandals.
- COSO framework requirements emphasize that management must establish governance structures aligned with organizational risk profiles and regulatory compliance obligations. Through clearly defined accountability mechanisms, companies create the foundation for effective segregation of duties and other preventive controls.

3. Promote accountability and transparency
- Accountability and transparency serve as fundamental deterrents against the misconduct that leads to securities class actions and regulatory enforcement. Management environments that fail to demonstrate genuine commitment to accountability consistently experience higher rates of fraud and compliance failures.
-
- Accountability frameworks require systematic implementation:
-
- Performance measurement systems that include compliance metrics and ethical behavior indicators
-
- Consistent disciplinary actions when policies are violated, regardless of individual position or status
-
- Appropriate consequences for misconduct that demonstrate organizational commitment to integrity
-
- Recognition programs that reward employees who identify potential violations or strengthen internal controls
- Transparency enables data-driven decision-making while encouraging employees to identify and report potential accounting fraud before it escalates into securities litigation. Organizations operating without transparency face workflow disruptions and inconsistent compliance with regulatory requirements.
- Companies that maintain accountability and transparency attract higher-quality personnel while reducing their exposure to the corporate governance failures that trigger costly legal proceedings. This requires establishing communication systems that keep employees informed about compliance performance and emerging regulatory developments.
- Effective control environments depend on competent staff who understand their compliance responsibilities and remain committed to preventing the misconduct that devastates investor confidence. When properly implemented, these foundational elements support comprehensive internal control frameworks designed to prevent accounting fraud, ensure regulatory compliance, and protect organizations from securities litigation.
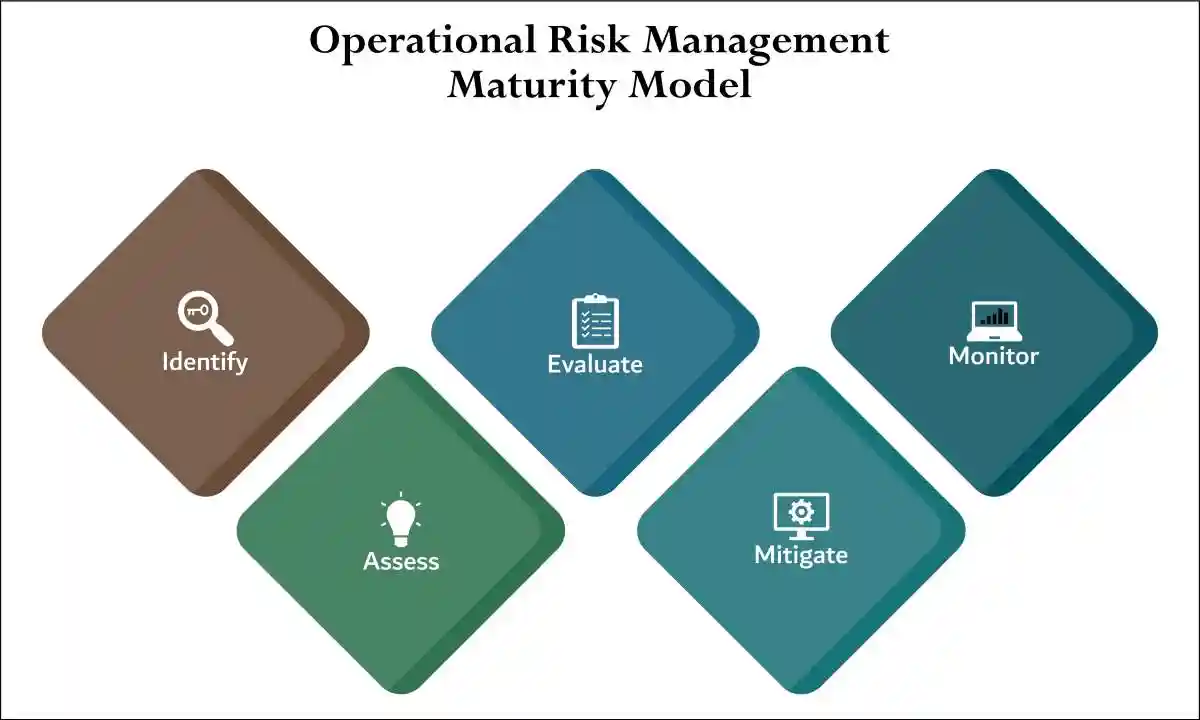
Step 2: Conduct a Comprehensive Risk Assessment
- Risk assessment serves as the critical second step in effective control implementation. After establishing a strong foundation through your control environment, conducting a thorough risk assessment becomes essential for identifying potential threats that could impede organizational objectives.
1. Identify internal and external risks
- Risk identification requires a systematic approach to uncover vulnerabilities from both inside and outside your organization. Effective risk identification involves examining various categories:
- Internal risks originate within your organization and typically include:
-
- Human factors: Employee errors, misconduct, insufficient training, or inadequate staffing
-
- Technological issues: System failures, outdated equipment, or inadequate IT infrastructure
-
- Business processes: Inefficiencies or outdated procedures
- External risks stem from outside sources beyond your direct control:
-
- Economic changes: Market fluctuations, inflation, or recessions
-
- Political factors: Changes in government policies or regulations
-
- Environmental threats: Natural disasters or resource scarcity
-
- Technological disruptions: Innovations that affect your business model
- To identify these risks effectively, utilize various techniques including brainstorming sessions with key stakeholders, interviews with subject matter experts, analysis of historical data, and review of incident reports. Subsequently, document these identified risks in a risk register for comprehensive tracking and management.
2. Evaluate fraud and compliance risks
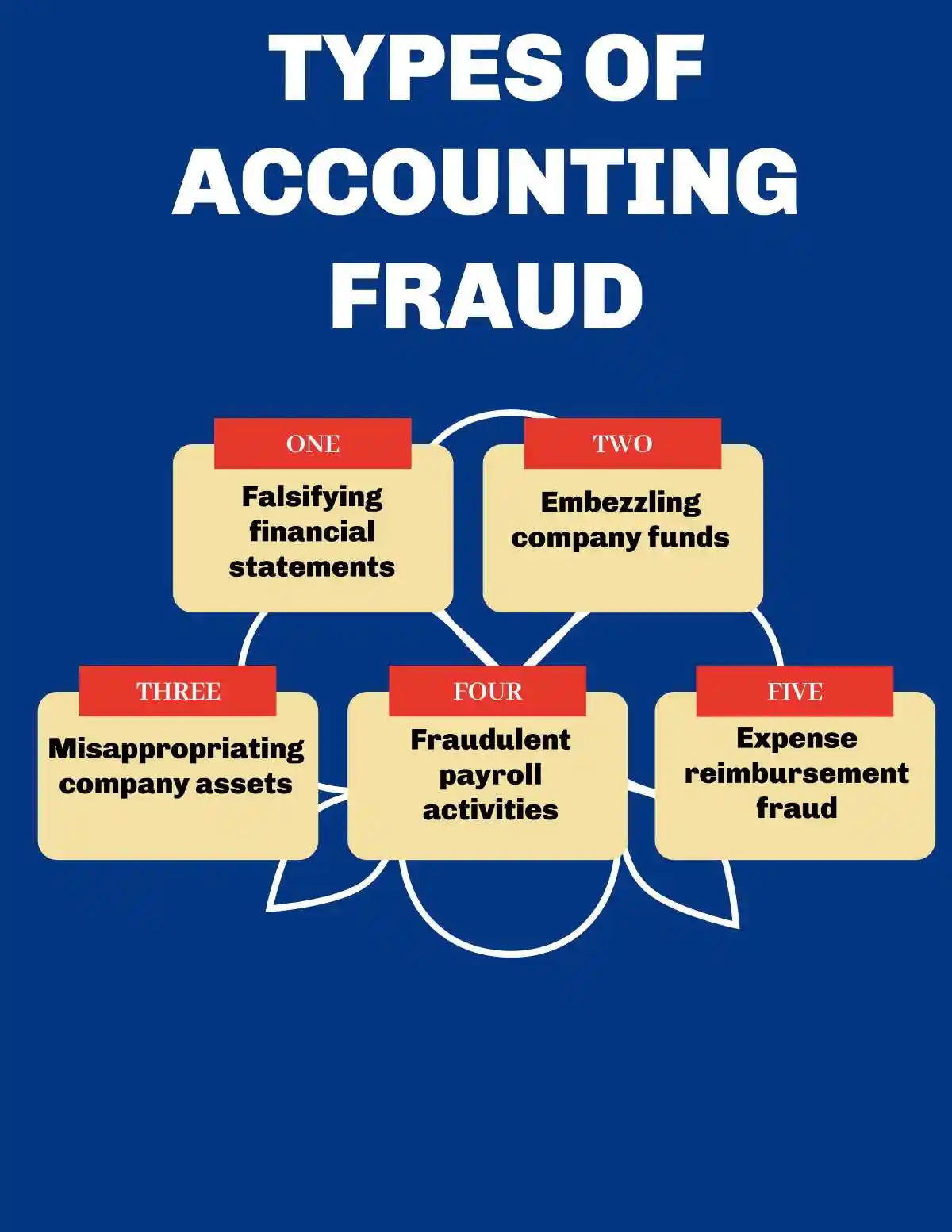
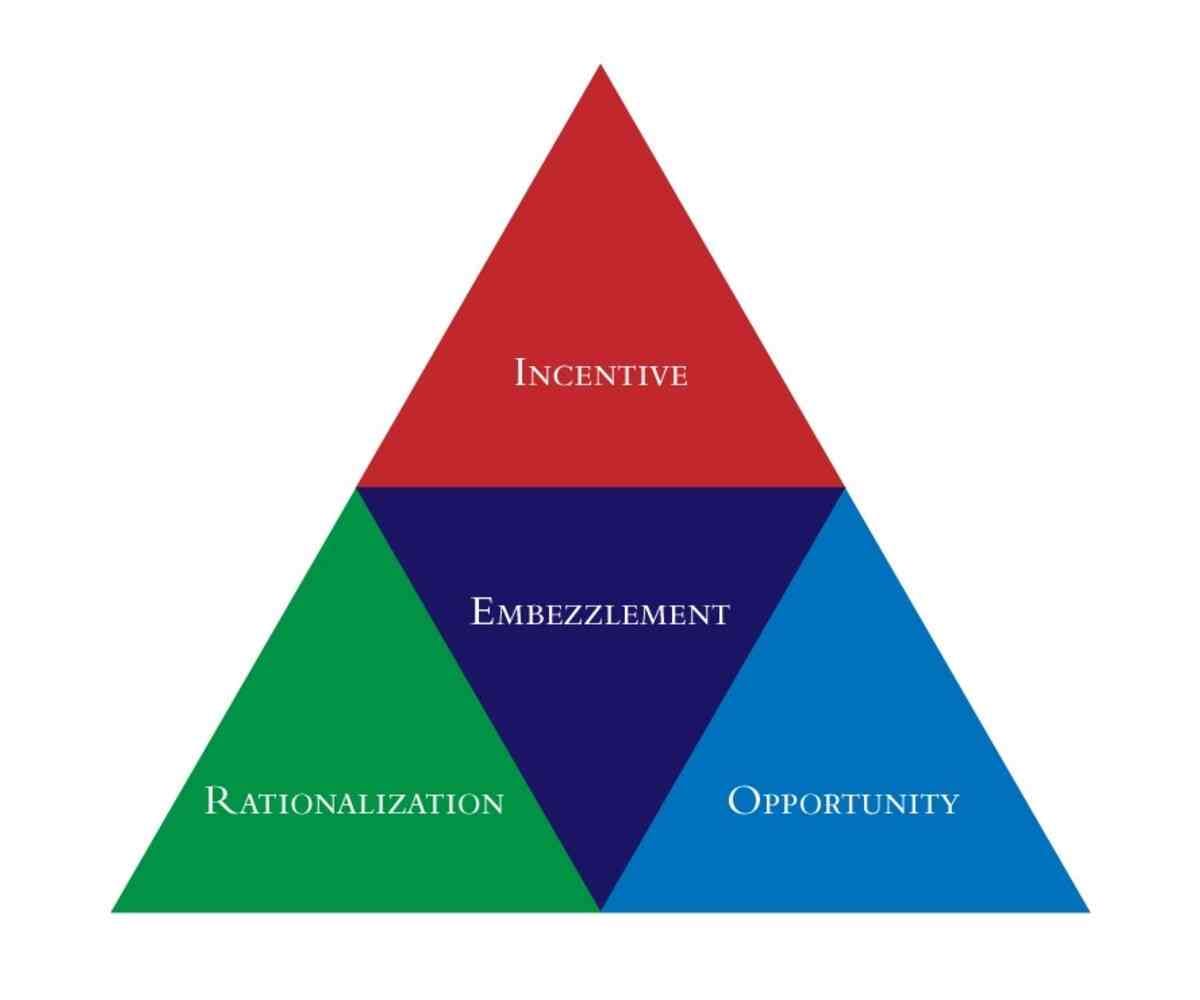
- Fraud risk represents a specific yet significant category that warrants special attention during your assessment. Fraud may be characterized as an intentional act, misstatement, or omission designed to deceive others, resulting in victim loss or perpetrator gain.
- Fraud typically falls into two main categories:
-
- Internal fraud: Committed by directors, employees, former employees, or engaged third parties
- External fraud: Includes first-party fraud (external parties against the organization) and victim fraud (when clients become victims of fraudulent acts)
- The true cost of fraud typically exceeds direct financial loss, given investigation time, productivity loss, and potential legal and compliance costs associated with remediation. Consequently, management should assess both likelihood and impact of potential fraud schemes to inform the design of risk management systems.
- During compliance risk evaluation, examine factors that influence fraud risk, including:
-
- The nature of your business and operating environment
-
- The effectiveness of existing internal controls
- Consider incentives, pressures, and opportunities that might enable fraud, as well as anti-fraud controls already in place. Specifically, evaluate the risk of management override of controls and potential regulatory misconduct.
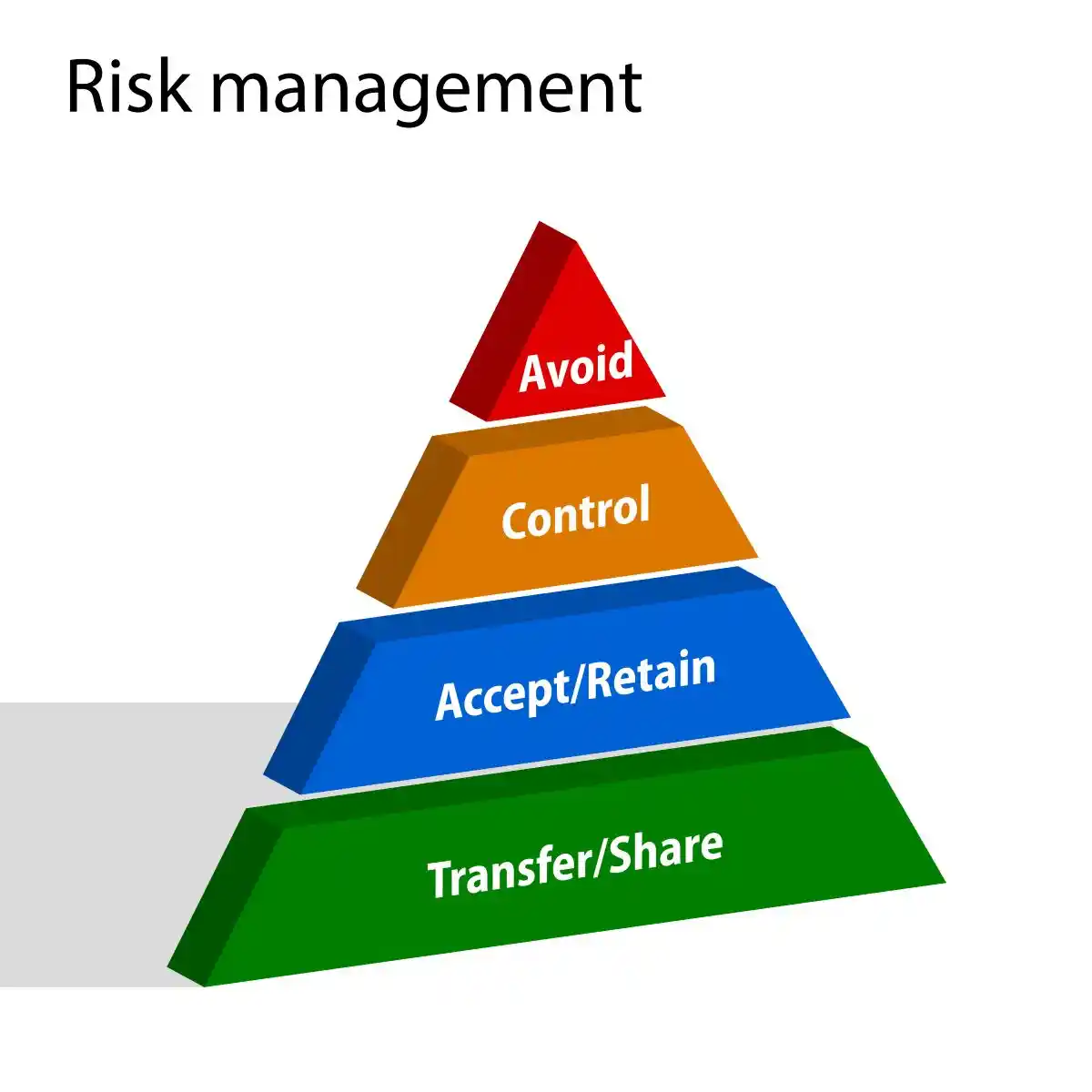
3. Prioritize risks based on impact and likelihood
- After identification and evaluation, prioritize risks to allocate resources effectively. This prioritization involves assessing both:
-
- Likelihood: The probability of risk occurrence
-
- Impact: The potential severity if the risk materializes
- A risk assessment matrix provides an effective tool for this purpose. This matrix plots risks on a grid with likelihood on one axis and impact on the other, enabling visual identification of high, medium, and low-priority risks.
- Most organizations employ a three-part scale (high, medium, low) or a more granular 5×5 matrix where 1 represents extremely low risk and 5 represents extremely high risk. This approach facilitates more efficient resource allocation by highlighting which risks require immediate attention.
- When assessing likelihood, consider:
-
- Prevalence of the risk in your industry
- Number of people involved in relevant processes
- For impact assessment, evaluate:
-
- Financial condition of your organization
-
- Value of threatened assets
-
- Potential criminal, civil, and regulatory liabilities
- Document your risk prioritization methodology in policy and procedure documents to maintain consistency across your organization. Ultimately, this comprehensive risk assessment process enables informed decisions about control implementation and resource allocation based on a clear understanding of your organization’s risk landscape.
Step 3: Design and Implement Control Activities
- Control activities represent the operational backbone of fraud prevention, directly addressing vulnerabilities that have historically led to corporate scandals and massive investor settlements. These systematic procedures transform abstract risk assessments into concrete protective measures that prevent accounting fraud before it can trigger securities class action lawsuits.
1. Segregation of Duties
- Segregation of duties serves as the primary defense against employee fraud and represents a cornerstone requirement under Sarbanes-Oxley Act provisions. This fundamental principle prevents any single individual from controlling entire transactions, eliminating opportunities for manipulation that have devastated companies like Enron and WorldCom.
- Effective segregation requires strict separation of four critical functions:
-
- Authorization – approving transactions and commitments
-
- Custody – maintaining physical control over assets
-
- Record keeping – documenting financial transactions
-
- Reconciliation – verifying accuracy and completeness
- Organizations that fail to maintain proper segregation create dangerous vulnerabilities. No individual should possess the authority to initiate, approve, record, and reconcile transactions simultaneously. The employee who requests inventory purchases cannot approve those same purchases, and purchasing approvers must remain separate from individuals who reconcile monthly vendor statements.
- Without these separations, companies expose themselves to embezzlement schemes and financial statement manipulation that can trigger costly regulatory enforcement actions.
2. Authorization and Approval Processes
- Strong authorization protocols create multiple checkpoints that make fraudulent activities significantly more difficult to execute and conceal. These processes establish clear delegation of authority while ensuring transactions meet established compliance standards before execution.
- Robust authorization frameworks require:
-
- Written documentation of authority levels and approval thresholds
-
- Dollar limits requiring escalated approvals for significant transactions
-
- Thorough review of supporting documentation by qualified approvers
-
- Prohibition of shared passwords or electronic signature credentials
- Effective approvers examine supporting documentation, question unusual transactions, and verify compliance with regulatory requirements and company policies. When approvers fail to exercise proper diligence, organizations become vulnerable to accounting irregularities that can escalate into serious legal problems.
- Authorization failures often serve as the foundation for subsequent securities litigation when investors discover that inadequate controls allowed fraudulent transactions to occur.3. Physical and Digital Access Controls
- Secure access controls protect sensitive information and critical business processes from unauthorized manipulation. These technical safeguards become particularly crucial when preventing accounting fraud and maintaining the internal controls required under federal securities regulations.
Physical security measures should include:
-
- Multi-factor authentication for accessing sensitive areas
-
- Biometric verification systems for critical locations
-
- Surveillance iintegration with access control systems
-
- Progressive security restrictions based on sensitivity levels
- Digital access controls must address privilege management, role-based permissions, and span-of-control limitations. These systems prevent unauthorized access to financial systems while ensuring employees can only perform functions appropriate to their designated roles. Organizations with weak digital controls face increased risk of data manipulation that can lead to financial statement fraud and subsequent securities class action exposure.
4. Documentation and Recordkeeping
- Comprehensive documentation creates the audit trail necessary to demonstrate regulatory compliance and detect potential fraud schemes. Without proper recordkeeping, organizations cannot prove they maintained adequate internal controls, leaving them vulnerable to regulatory sanctions and investor litigation.
- Essential documentation must include:
-
- Written policies detailing specific control procedures
-
- Clear assignment of responsibilities and authority limitations
-
- Records documenting control performance and identified exceptions
-
- Evidence of proper approvals and authorizations for all transactions
- Accurate recordkeeping functions as both preventive and detective control mechanisms. Proper documentation prevents errors by establishing standard procedures, while creating evidence that enables detection of problems after they occur. Records should identify primary and backup responsible parties, escalation procedures, and oversight mechanisms that ensure accountability throughout the organization.
- Control design must balance fraud prevention with operational efficiency. Excessive controls can impede business operations, while insufficient controls expose organizations to significant accounting fraudrisks and potential securities litigation. Focus control resources on addressing the highest-priority risks identified during comprehensive risk assessment processes.
Step 4: Build Effective Information and Communication Systems
- Information and communication systems serve as the operational backbone that connects all elements of your internal control system and enables effective regulatory compliance monitoring. Communication breakdowns represent one of the most common factors in corporate governance failures, as organizations cannot detect or respond to control deficiencies without reliable information flow.
- Companies with robust communication frameworks identify control weaknesses 60% faster than organizations with fragmented information systems. This rapid detection capability proves essential for preventing minor control issues from escalating into serious compliance violations that trigger regulatory enforcement actions.
1. Ensure timely internal communication
- Internal communication facilitates the flow of critical compliance information throughout your organization, enabling personnel to understand their responsibilities and execute controls effectively. Effective communication prevents the information gaps that historically preceded major corporate scandals.
- Essential internal communication requirements include:
-
- Policy accessibility: Make internal control policies and procedures readily available to all personnel through centralized systems
-
- Standardized channels: Create defined communication pathways with clear purposes and accountability structures
-
- Regular updates: Implement consistent timing for control performance reporting and risk alerts
-
- Whistleblower channels: Establish separate, protected communication lines for reporting concerns without fear of retaliation
- Organizations cannot realize the benefits of their internal control investments without open communication channels that support control implementation. Compliance teams frequently lack visibility into all risk areas and control functions, preventing them from identifying critical gaps in the control environment.
- Your internal communication strategy must address these fundamental questions:
-
- Does your department receive timely information from internal and external sources?
-
- Does your department receive alerts about emerging compliance risks?
-
- Does your department access performance measurement data for control effectiveness?
-
- Are responsibilities and accountability structures documented and communicated effectively?
- Knowledge workers switch between different applications up to 1,200 times daily. Communication systems must balance accessibility with security requirements, as overly complex tools undermine control effectiveness and employee compliance.
2. Establish external reporting channels
- External communication operates bidirectionally, supporting both regulatory reporting obligations and stakeholder relations that influence corporate governance effectiveness. These channels prove fundamental for maintaining regulatory compliance and avoiding enforcement actions.
- External communication must be established with:
-
- Suppliers and contractors subject to compliance requirements
-
- Service organizations handling sensitive data or processes
-
- External auditors conducting internal control assessments
-
- Effective external reporting requires clear terms, conditions, privacy policies, and]service agreements that communicate responsibilities and regulatory expectations.
-
- Creating accessible channels for external parties to report system failures, incidents, or
- Regulatory reporting helps ensure your organization manages data and operations in compliance with applicable laws and industry standards. Structured reporting mechanisms create accountability and audit trails while fulfilling disclosure obligations that support broader internal control objectives.
3. Use secure and reliable data systems
- Secure data systems form the technological foundation of effective internal controls, protecting sensitive information while ensuring availability for compliance monitoring and regulatory reporting. These systems must meet both operational needs and regulatory security standards.
- Essential data control mechanisms include:
- Encryption and access controls protecting sensitive financial and operational data
- Firewalls and security protocols preventing unauthorized access
- Regular data backup procedures ensuring continuity during incidents
- Disaster recovery mechanisms maintaining operations during disruptions
- Timely data disposal procedures meeting regulatory requirements
- Implement role-based access controls ensuring only authorized individuals can access specific information categories. Protection measures should include password requirements, multi-factor authentication, and systematic access control reviews.
- Data management tools should automate control processes when possible, reducing human error risks while improving compliance monitoring efficiency. Regular system updates and maintenance protect against emerging vulnerabilities that could compromise your control environment.
- Formal and informal communication channels both contribute to effective internal controls. Formal systems range from ssophisticated compliance monitoring technology to structured management meetings, while informal stakeholder conversations often provide critical insights for identifying emerging risks and opportunities. This balanced approach ensures decision-makers receive timely information for effective risk management.
- The COSO framework emphasizes three core principles for information and communication systems: utilizing quality data for decision-making, facilitating internal communication across all organizational levels, and maintaining transparent external communication with relevant parties. Proper implementation of these principles enables your control systems to operate effectively while supporting organizational objectives and regulatory compliance strategies.
Step 5: Monitor and Evaluate Control Effectiveness
- Monitoring activities serve as the essential early warning system that detects control failures before they escalate into accounting fraud scandals and trigger devastating securities class action lawsuits. Organizations with inadequate monitoring face substantially higher risks of undetected fraud, with corporate scandals typically emerging years after initial control breakdowns occur.
- Research shows that organizations with robust monitoring processes identify control weaknesses 60% faster than those with ad hoc approaches, often preventing minor issues from becoming major regulatory enforcement actions.
1. Perform regular audits and reviews
- Systematic auditing provides the foundation for detecting financial statement fraudbefore it reaches the materiality thresholds that trigger securities litigation. These evaluations determine whether internal controls operate as designed and effectively prevent the types of misconduct that have historically led to massive investor settlements. Organizations must implement two complementary monitoring approaches:
-
- Ongoing monitoring activities function as continuous oversight mechanisms that assess control effectiveness during normal business operations, identifying anomalies that might indicate emerging fraud schemes. These real-time evaluations catch problems early, before they can develop into the sophisticated schemes that have devastated companies like Enron and WorldCom.
-
- Separate evaluations include formal internal audits and departmental self-assessments that produce documented evidence of control effectiveness. These periodic reviews create the audit trail necessary to demonstrate regulatory compliance and defend against allegations of inadequate oversight in securities litigation.
- Risk-focused monitoring concentrates resources on high-risk areas where control failures could significantly damage organizational objectives and trigger corrective disclosures. This targeted approach ensures that monitoring efforts address the most vulnerable areas first, preventing the cascade of failures that typically characterizes major corporate scandals.
- Management responses to audit findings require immediate implementation of corrective measures to address identified deficiencies. Audit reports establish timelines for resolving these issues, with follow-up verification to ensure proper remediation. High-risk control areas demand continuous monitoring even after initial corrections, as these represent the greatest threats to investor confidence and regulatory compliance.
2. Track corrective actions
- Corrective action management transforms audit findings into concrete improvements that strengthen the organization’s defense against fraud and misconduct. Failure to properly track and implement corrective measures has been a common factor in major corporate governance failures that resulted in hundreds of millions in securities class action settlements.
- Automated tracking systems provide sophisticated tools for monitoring remediation efforts and ensuring compliance with regulatory standards such as Sarbanes-Oxley requirements. These systems create the documentation trail necessary to demonstrate proactive risk management when facing regulatory enforcement investigations.
- Lifecycle management systems automate the entire corrective process from identification through final closure, preventing the gaps in oversight that have historically allowed control problems to persist undetected. Organizations with comprehensive tracking systems demonstrate their commitment to maintaining effective internal controls that protect investor interests.
- Integration with compliance processes connects corrective actions to broader corporate governance initiatives, creating a holistic approach to risk mitigation that addresses systemic vulnerabilities. This integration ensures that isolated control fixes contribute to enterprise-wide improvements in regulatory compliance and fraud prevention.
- Organizations must establish transparent escalation procedures that prioritize critical issues based on their potential impact on financial reporting and investor protection. Clear communication protocols ensure that serious control deficiencies receive immediate attention before they can trigger the types of problems that lead to securities litigation.
3. Use performance metrics and dashboards
- Performance monitoring systems provide real-time visibility into control effectiveness, enabling management to identify emerging risks before they develop into material weaknesses that compromise financial reporting integrity. These systems transform abstract control concepts into concrete metrics that demonstrate regulatory compliance and support corporate governance objectives.
- Key Performance Indicators establish measurable standards for control performance, creating benchmarks that help identify when corrective actions become necessary. Well-designed KPIs provide early warning signals that prevent minor control issues from escalating into the types of systematic failures that have triggered major accounting fraud investigations.
- Visual monitoring tools present complex control data in formats that enable quick identification of trends and anomalies that might indicate emerging fraud risks. These dashboards help management maintain constant oversight of critical control functions without becoming overwhelmed by excessive detail.
- Real-time monitoring capabilities enable immediate responses to control breakdowns, preventing the delays that have allowed fraud schemes to grow undetected in numerous corporate scandals. This immediate awareness supports the rapid intervention necessary to maintain investor confidence and avoid regulatory enforcement actions.
- Comprehensive performance monitoring systems create dynamic oversight capabilities that continuously measure control effectiveness, detect performance outliers, analyze root causes of control failures, and support strategic planning for risk management improvements. This data-driven approach ensures that monitoring activities provide tangible business value rather than merely satisfying compliance requirements.
Step 6: Align Controls with Corporate Governance and Compliance
- Corporate governance frameworks provide the regulatory foundation that determines whether internal controlswill successfully protect organizations from securities litigation and regulatory enforcement actions. Organizations that fail to align control systems with applicable regulatory requirements face substantial penalties, including SEC sanctions exceeding $4 million and devastating securities class action lawsuits that can destroy shareholder value overnight.
1. Integrate with Regulatory Frameworks
- Regulatory compliance requires systematic integration of control activities with established governance frameworks that define transparency, accountability, and ethical decision-making standards. These frameworks serve as the legal foundation upon which effective internal controls must be built to withstand regulatory scrutiny.
- Control integration demands:
-
- Breaking down framework elements according to functional areas and combining related control families
-
- Identifying critical controls that address the most restrictive regulatory requirements
-
- Defining control numbering systems and nomenclature for systematic evaluation and tracking
-
- Reducing data scope strategically, as each control element represents significant investment in resources
- Mergers and acquisitions create immediate compliance vulnerabilities. Companies must engage in prompt, risk-based reviews of accounting and disclosure controls after transactions, as no “grace period” exists for maintaining effective controls following acquisitions. Regulatory enforcement agencies monitor these transitions closely, making integration failures a primary target for enforcement actions.
2. Support SEC Enforcement and Reporting
- The Securities and Exchange Commission actively enforces federal securities laws through its Enforcement Division, which protects investors by investigating violations and pursuing enforcement actions against companies with inadequate internal controls. Recent enforcement priorities focus on cybersecurity disclosure failures, materiality determination weaknesses, and information capture deficiencies.
- SEC enforcement actions highlight critical control requirements:
-
- Policies and procedures must facilitate prompt escalation of cybersecurity incidents to disclosure decision-makers. Control systems must support timely materiality determinations for all significant business events. Information capture and reporting mechanisms must operate with complete accuracy.
-
- Penalty structures range from $990,000 to $4 million for disclosure control violations, though exemplary cooperation and comprehensive remediation can result in reduced penalties or lesser charges. Companies demonstrating proactive regulatory compliance receive more favorable treatment during enforcement proceedings.
3. Address Securities Litigation Risks
- Securities litigation exposes public companies to massive financial liabilities, with average settlement amounts reaching $68 million. These cases typically emerge following stock price declines when shareholders allege that decreases reflect previously concealed information that should have been disclosed through proper internal controls.
- Protection strategies require:
-
- Effective disclosure controls combined with cultures of compliance that prevent securities litigation from materializing. Adequate accounting personnel with clear communication lines prevent breakdowns between subject matter experts and disclosure decision-makers. Investment in suitable, experienced accounting staff reduces the likelihood of control failures that trigger investor lawsuits.
-
- SEC enforcement increasingly targets internal accounting and disclosure control violations as primary bases for regulatory actions. Organizations must establish and maintain effective systems of internal control over financial reporting to avoid financial restatements, delayed filings leading to exchange delisting, and unchecked employee misconduct that creates massive litigation exposure.
Step 7: Technology Solutions for Enhanced Control Monitoring
- Technology automation eliminates the manual processes that historically created vulnerabilities exploited in major corporate fraud cases. Modern control environments require sophisticated technological tools to detect accounting irregularities and prevent the financial statement manipulation that triggers devastating securities class action lawsuits.
1. Use GRC and ERP tools
- Governance, Risk, and Compliance (GRC) and Enterprise Resource Planning (ERP) systems provide essential infrastructure for automated fraud detection and regulatory compliance. These integrated platforms eliminate the reconciliation gaps that fraudsters exploit while creating comprehensive audit trails that satisfy SEC enforcement requirements.
- GRC tools enable organizations to:
-
- Establish proactive risk management programs that identify fraud risks before they escalate
-
- Automate compliance processes required under federal securities regulations
-
- Manage regulatory changes that affect internal control requirements
-
- Implement systematic governance procedures that prevent corporate governance failures
- ERP implementations represent critical opportunities to replace manual controls vulnerable to manipulation with automated systems that create real-time fraud detection capabilities. Companies that fail to implement proper security monitoring during ERP transitions expose themselves to significant operational risks and potential securities litigation.
- Organizations must evaluate vendor reputation and ongoing support capabilities, as system failures can create internal control weaknesses that trigger regulatory investigations.
2. Implement robotic process automation
- Robotic Process Automation (RPA) eliminates the human error risks that contribute to accounting fraud by automating repetitive financial processes through software robots that execute transactions with precision and consistency. These digital systems create immutable records that strengthen audit trails and support regulatory compliance efforts.
- RPA delivers measurable benefits for fraud prevention:
-
- Processes financial transactions faster than manual systems while maintaining accuracy
-
- Eliminates data entry errors that create vulnerabilities exploited in financial manipulation schemes
-
- Executes control procedures with consistency that prevents the irregularities investigated in SEC enforcement actions
- Successful RPA implementation requires systematic evaluation of automation opportunities, careful vendor selection, detailed process documentation, controlled pilot testing, and ongoing lifecycle management. Organizations must recognize that RPA enhances rather than replaces human oversight responsibilities in maintaining effective internal controls.
3. Monitor controls with data analytics
- Data analytics transforms traditional control monitoring by enabling comprehensive population testing that identifies financial statement fraud patterns invisible to sampling-based approaches. Advanced analytical tools provide real-time fraud detection capabilities that support timely corrective disclosure when irregularities are discovered. Data visualization presents complex fraud risk information in formats that enable management to make informed decisions about risk mitigation strategies.
- Data analytics enables organizations to test entire transaction populations rather than statistical samples. Companies implementing proactive data monitoring systems experience 52% lower fraud losses compared to organizations relying on traditional detection methods. Analytics platforms simultaneously test multiple fraud indicators across massive datasets, completing in minutes the analysis that previously required weeks of manual review.
- Modern control monitoring requires dual analytical capabilities:
-
- Real-time monitoring systems that capture transaction data from business systems and immediately flag unusual patterns based on fraud risk indicators established by the organization
-
- Continuous remediation monitoring that integrates comprehensive business data across multiple systems to create comprehensive risk dashboards supporting ongoing corporate governance oversight
-
- Real-time data analytics enables organizations to understand current fraud risks and formulate targeted strategies for internal control optimization that prevent the control failures leading to securities class action lawsuits.
Step 8: Train Staff and Build a Control-Conscious Culture
- Employee training represents the final critical element in preventing accounting fraud and avoiding the costly securities class action lawsuits that devastate companies with inadequate control systems. Organizations with comprehensive training programs experience significantly lower fraud losses and maintain stronger defenses against the regulatory enforcement actions that can destroy corporate reputations and shareholder value.
1. Conduct Regular Training Programs
- Control systems training must establish baseline knowledge requirements that directly address fraud prevention and regulatory compliance obligations. Companies face substantial legal liability when employees lack proper understanding of internal controls and their role in preventing financial misstatements that trigger securities litigation.
- Effective training programs include these essential components:
-
- Identification of minimum knowledge requirements for fraud detection and prevention
-
- Verification methods to ensure employees understand their compliance responsibilities
-
- Continued reinforcement through periodic re-qualification that addresses emerging fraud schemes
- Operational excellence depends on personnel who can respond appropriately when they encounter potential accounting irregularities or pressure to manipulate financial results. Training programs must prepare employees to recognize warning signs of fraud and understand the severe consequences of participating in schemes that violate securities laws.
2. Promote Awareness Through Campaigns
- Security awareness campaigns tailored to specific risk profiles help employees understand how their roles connect to broader fraud prevention efforts. These targeted approaches address the reality that different employee groups face distinct pressures and opportunities for misconduct.
- Awareness campaigns should focus on these priorities:
-
- Engage leadership through workshops that emphasize legal consequences of control failures
-
- Partner with communication teams to deliver consistent messaging about fraud prevention
-
- Align training content with organizational values while highlighting regulatory requirements
- Data-driven programming enables organizations to measure campaign effectiveness and demonstrate compliance with oversight requirements. Gamification elements maintain employee engagement while reinforcing critical concepts about internal controls and ethical conduct.
3. Encourage Reporting and Feedback
- Open communication channels serve as essential early warning systems that can prevent minor control weaknesses from escalating into major fraud schemes that result in securities class actions. Employees must understand their protection under whistleblower statutes and feel confident that reporting concerns will not result in retaliation.
- Feedback mechanisms require systematic approaches that connect employee observations to risk management processes:
-
- Train managers to receive and respond to concerns about potential accounting fraud or control deficiencies
-
- Equip compliance teams with skills to investigate reports and implement corrective measures
-
- Provide ongoing education about legal protections available to employees who report misconduct
-
- Regular follow-up demonstrates organizational commitment to maintaining effective internal controls and preventing the corporate scandals that destroy stakeholder trust. Feedback systems must create accountability at every organizational level while encouraging early identification of problems before they result in material misstatements.
- Control-conscious culture emerges when employees understand that their individual actions contribute to preventing financial statement fraudand protecting the organization from devastating legal consequences that can result in massive settlements and regulatory sanctions.
Securities Litigation and Class Action Consequences
- When accounting fraud occurs, affected investors often seek recourse through securities class actions and securities litigation. These legal mechanisms provide a pathway for investors to recover losses resulting from materially misleading financial statements and other violations of federal securities laws.
- The securities litigation process typically begins when a company’s stock price declines following the disclosure of previously unknown negative information. If investors can demonstrate that the company made material misstatements or omissions in its financial reports, they may file a class action lawsuit seeking damages for their investment losses.
- Securities class actions related to financial statement fraud often result in substantial settlements. Recent cases have produced recoveries ranging from $50 million to over $500 million, depending on the scope of the fraud and the resulting investor losses. These settlements serve multiple purposes: they compensate injured investors, deter future misconduct, and reinforce the importance of accurate financial reporting.
- The legal consequences extend beyond civil litigation. Regulatory enforcement actions by the SEC can result in substantial monetary penalties, officer and director bars, and requirements for enhanced corporate governance measures. In severe cases, criminal prosecutions may result in prison sentences for executives who participated in fraudulent schemes.
THE SECURITIES LITIGATION PROCESS
| Filing the Complaint | A lead plaintiff files a lawsuit on behalf of similarly affected shareholders, detailing the allegations against the company. |
| Motion to Dismiss | Defendants typically file a motion to dismiss, arguing that the complaint lacks sufficient claims. |
| Discovery | If the motion to dismiss is denied, both parties gather evidence, documents, emails, and witness testimonies. This phase can be extensive. |
| Motion for Class Certification | Plaintiffs request that the court to certify the lawsuit as a class action. The court assesses factors like the number of plaintiffs, commonality of claims, typicality of claims, and the adequacy of the proposed class representation. |
| Summary Judgment and Trial | Once the class is certified, the parties may file motions for summary judgment. If the case is not settled, it proceeds to trial, which is rare for securities class actions. |
| Settlement Negotiations and Approval | Most cases are resolved through settlements, negotiated between the parties, often with the help of a mediator. The court must review and grant preliminary approval to ensure the settlement is fair, adequate, and reasonable. |
| Class Notice | If the court grants preliminary approval, notice of the settlement is sent to all class members, often by mail, informing them about the terms and how to file a claim. |
| Final Approval Hearing | The court conducts a final hearing to review any objections and grant final approval of the settlement. |
| Claims Administration and Distribution | A court-appointed claims administrator manages the process of sending notices, processing claims from eligible class members, and distributing the settlement funds. The distribution is typically on a pro-rata basis based on recognized losses. |
Conclusion
- Control implementation represents a fundamental business imperative that extends far beyond mere compliance requirements. Organizations that fail to establish robust internal control frameworks expose themselves to catastrophic risks, including devastating securities class action lawsuits, regulatory enforcement actions, and permanent damage to market credibility.
- Preventative controls and detective controls form the essential architecture that protects organizations from the financial and reputational destruction that follows corporate scandals. Companies with effective control environments demonstrate measurably lower fraud losses while maintaining the investor confidence necessary for sustained market performance. The evidence remains clear: organizations that prioritize control implementation outperform their peers in virtually every measurable category.
- Key implementation priorities include establishing ethical leadership structures, conducting thorough risk assessments that prioritize the most consequential vulnerabilities, and designing targeted control activities that address specific fraud schemes. Information systems must support real-time monitoring capabilities while maintaining regulatory compliance with evolving enforcement standards. Technology integration enhances control effectiveness through automation and advanced analytics that detect anomalies before they escalate into serious legal issues.
- Control implementation demands continuous adaptation rather than static compliance efforts. Risk assessment methodologies must evolve alongside changing business conditions and emerging fraud patterns. Companies that treat controls as annual exercises rather than ongoing strategic priorities inevitably face the consequences when their outdated systems fail to detect sophisticated schemes.
- Employee training and cultural development prove equally critical as technical control design. The most sophisticated internal controls cannot prevent fraud without knowledgeable personnel who understand their roles in maintaining organizational integrity. Whistleblower programs and open communication channels enable early detection of problems before they trigger costly corrective disclosures and subsequent litigation.
- The investment required for effective internal controls represents a fraction of the costs associated with corporate scandals and their aftermath. Securities litigation settlements routinely exceed hundreds of millions of dollars, while regulatory penalties and reputational damage can permanently impair organizational viability. The cost of prevention invariably proves far less than the price of remediation, making proactive control implementation not just a legal necessity buy a sound business strategy that protects all stakeholders’ interests.
- Market integrity depends fundamentally on organizations that maintain transparent, accountable operations through robust internal controls. These systematic safeguards protect not only individual companies but also the broader financial system upon which investors, creditors, and regulators rely for accurate information and ethical conduct.
Key Takeaways
Implementing effective internal controls requires a systematic eight-step approach that transforms organizational risk management from reactive to proactive, protecting assets while enabling sustainable growth.
• Establish ethical leadership first: Strong control environments begin with clear “tone at the top” where executives demonstrate integrity through actions, not just policies, creating accountability throughout the organization.
• Prioritize risks strategically: Focus control resources on high-impact, high-likelihood risks using assessment matrices rather than attempting to control everything equally.
• Separate duties to prevent fraud: Implement segregation of duties by dividing authorization, custody, record-keeping, and reconciliation functions among different individuals to eliminate single-person control over transactions.
• Leverage technology for automation: Use GRC tools, ERP systems, and robotic process automation to reduce human error, increase consistency, and enable real-time monitoring of control effectiveness.
• Monitor continuously, not periodically: Combine ongoing monitoring activities with regular audits, performance dashboards, and corrective action tracking to ensure controls remain effective as business conditions change.
• Build control-conscious culture: Train staff regularly and encourage open reporting channels, as even the most sophisticated controls fail without knowledgeable employees who understand their importance and application.
Remember that control implementation is an ongoing process requiring annual revisions aligned with risk assessments. Organizations with robust internal controls experience 52% lower fraud losses and faster detection of control weaknesses, making this investment essential for long-term organizational success.
FAQs
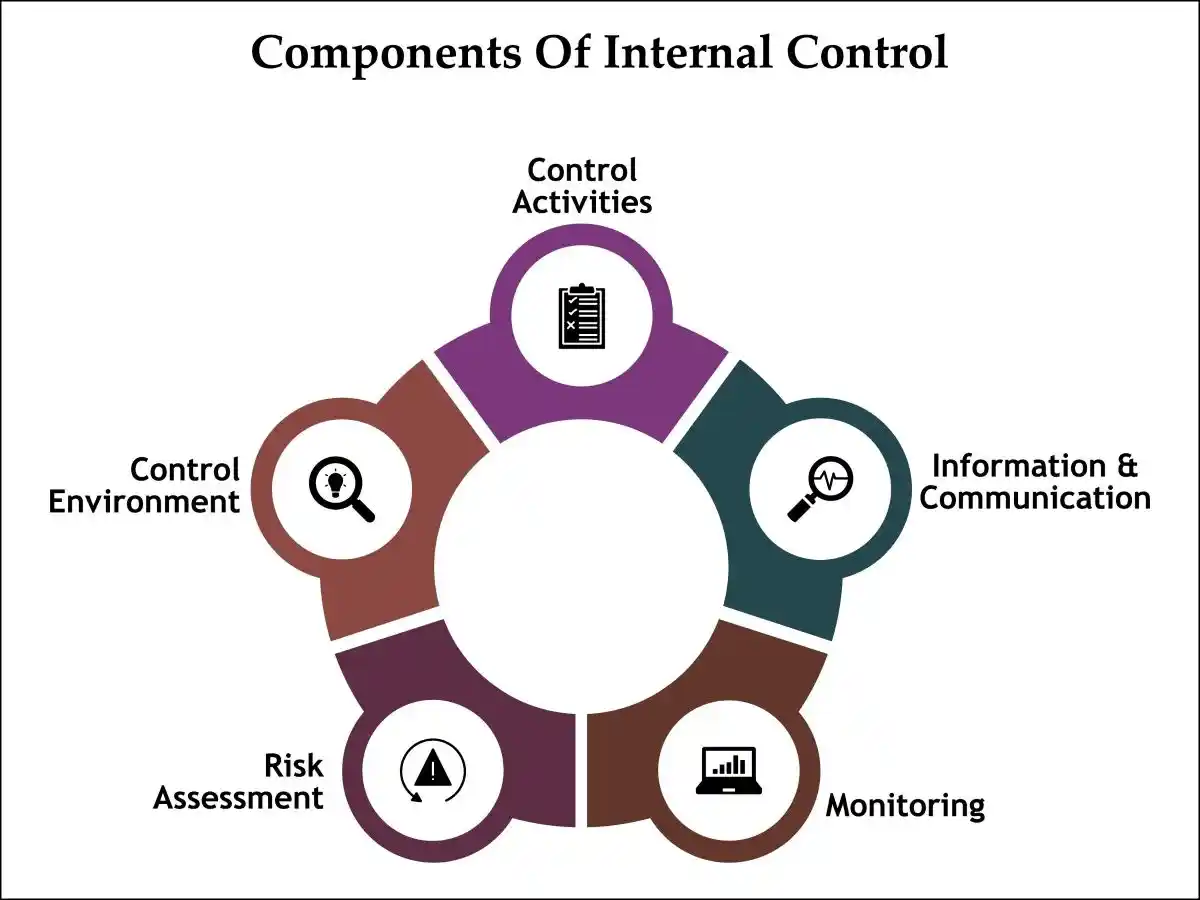
Q1. What are the key components of an effective internal control system? An effective internal control system consists of five key components: control environment, risk assessment, control activities, information and communication, and monitoring. These work together to create a comprehensive framework for managing risks and achieving organizational objectives.
Q2. How often should internal controls be reviewed and updated? Internal controls should be reviewed and updated at least annually. However, more frequent reviews may be necessary in rapidly changing business environments or after significant organizational changes like mergers or acquisitions.
Q3. What role does technology play in modern internal control implementation? Technology plays a crucial role in modern internal control implementation by enabling automation of control activities, enhancing monitoring capabilities through data analytics, and improving communication across the organization. Tools like GRC software, ERP systems, and robotic process automation can significantly increase the efficiency and effectiveness of controls.
Q4. How can organizations foster a culture that supports effective internal controls? Organizations can foster a control-conscious culture by setting a clear “tone at the top,” conducting regular training programs, promoting awareness through campaigns, and encouraging open communication and feedback. It’s crucial to create an environment where employees understand the importance of controls and feel comfortable reporting concerns.
Q5. What are the potential consequences of weak internal controls? Weak internal controls can lead to various negative consequences, including increased risk of fraud, financial misstatements, regulatory non-compliance, and operational inefficiencies. Organizations with inadequate controls may face financial losses, damage to reputation, legal penalties, and decreased stakeholder confidence.
Contact Timothy L. Miles Today for a Free Case Evaluation
If you suffered substantial losses and wish to serve as lead plaintiff in a securities class action, or have questions about securities class action settlements, or just general questions about your rights as a shareholder, please contact attorney Timothy L. Miles of the Law Offices of Timothy L. Miles, at no cost, by calling 855/846-6529 or via e-mail at [email protected]. (24/7/365).
Timothy L. Miles, Esq.
Law Offices of Timothy L. Miles
Tapestry at Brentwood Town Center
300 Centerview Dr. #247
Mailbox #1091
Brentwood,TN 37027
Phone: (855) Tim-MLaw (855-846-6529)
Email: [email protected]
Website: www.classactionlawyertn.com
Facebook Linkedin Pinterest youtube
Visit Our Extensive Investor Hub: Learning for Informed Investors